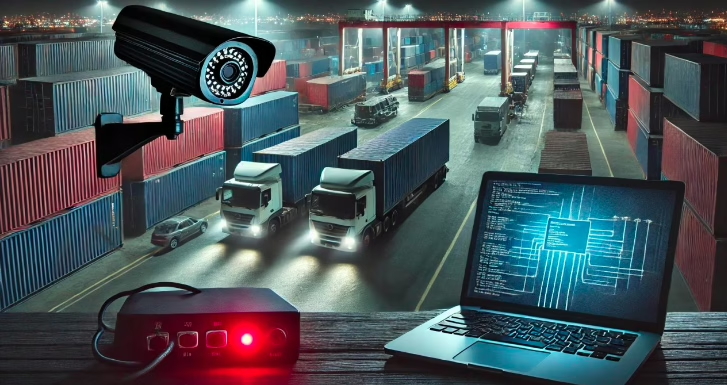
Have you heard of IoT SecOps? Your SecOps team may be defending the network… while risk (literally) walks in through Cameras, Badges and edge devices. The enterprise is no longer just digital. It’s cyber-physical. We know, badges integrate with identity … Read More
remote management

Relevance of SecOps Beyond IT to loT and Edge Assets

Asset Management Reinvented for the Intelligent Edge Era
Managing assets, whether physical devices, digital objects, or IoT endpoints—has always been central to operational success. As connectivity and technology continue to advance, asset management too has rapidly evolved, moving from labour intensive manual tracking to seamless, intelligent, and data-driven … Read More

Staying Compliant at the Edge is Tough, and Gaps Surface When You Least Expect Them
More devices, more regulations, more risks… and more pressure on teams to keep distributed IoT environments secure, audit-ready, and consistently aligned with policy. For most organizations, the reality is that current compliance practices aren’t built for this level of scale … Read More

Are you still stuck in the black-and-white era of security?
Author: Niranjan Maka Security service providers, while you and your teams were focused on protecting the perimeter, the world of security has undergone a massive evolution. It’s no longer just about “𝑤𝑎𝑡𝑐ℎ 𝑡ℎ𝑒 𝑝𝑒𝑟𝑖𝑚𝑒𝑡𝑒𝑟, 𝑡ℎ𝑟𝑜𝑢𝑔ℎ 𝑡ℎ𝑜𝑠𝑒 𝑐𝑎𝑚𝑒𝑟𝑎𝑠”. 𝑺𝒆𝒄𝒖𝒓𝒊𝒕𝒚 𝒉𝒂𝒔 𝒆𝒗𝒐𝒍𝒗𝒆𝒅 … Read More
Surprised? Not Surprising (Part 2)
Author: Niranjan Maka The Louvre Heist has been in the headlines. And CISO/CIO/CEOs don’t envy them. 𝑻𝒉𝒆 𝒍𝒂𝒕𝒆𝒔𝒕 𝒊𝒔 𝒕𝒉𝒆 𝒓𝒆𝒗𝒆𝒍𝒂𝒕𝒊𝒐𝒏 𝒕𝒉𝒂𝒕 “𝒔𝒕𝒂𝒏𝒅𝒂𝒓𝒅𝒊𝒔𝒆𝒅” 𝒄𝒓𝒆𝒅𝒆𝒏𝒕𝒊𝒂𝒍𝒔 𝒉𝒂𝒅 𝒃𝒆𝒆𝒏 𝒖𝒔𝒆𝒅 𝒂𝒕 𝒔𝒐𝒎𝒆 𝒑𝒐𝒊𝒏𝒕 𝒊𝒏 𝒎𝒂𝒏𝒂𝒈𝒊𝒏𝒈 𝒕𝒉𝒆𝒊𝒓 𝒔𝒆𝒄𝒖𝒓𝒊𝒕𝒚 𝒂𝒔𝒔𝒆𝒕𝒔 This is not surprising for … Read More
Top 6 Reasons Manufacturers Are Adopting AI at the Edge
Modern manufacturing is undergoing a massive transformation, pushed by the need for speed, precision, and always-on operations. Plants are becoming smarter, more connected, and far more data driven. And at the center of this shift is AI-driven edge automation and … Read More
Understanding Agentic AI: From Concept to an Application (Example)
You’ve probably encountered a wave of posts about Agentic AI lately. The enthusiasm is warranted – but often, clarity is missing. Or the focus is entirely on the tools/frameworks. For those from the last century, familiar with “Structured Systems Analysis” … Read More
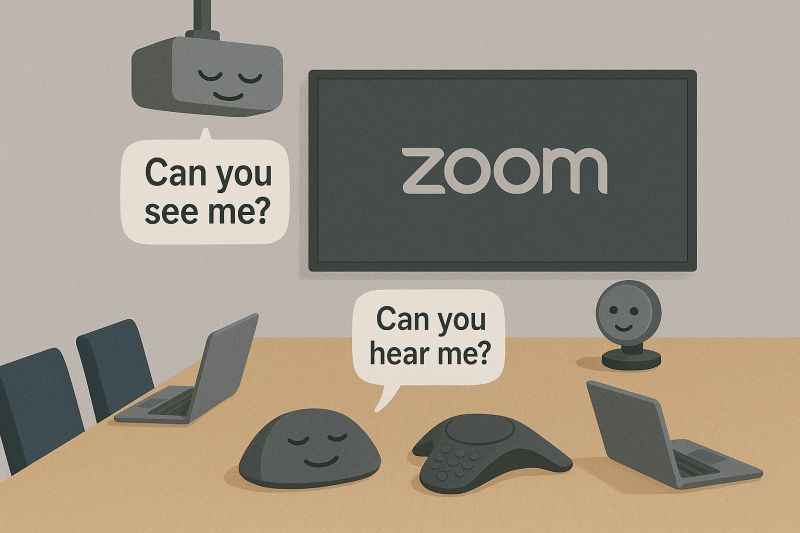
“Can you see me? Can you hear me?
The dreaded Monday morning chorus in hybrid meeting rooms. A frustrated IT manager put it best: 🗣️ “𝐻𝑎𝑙𝑓 𝑜𝑢𝑟 𝑒𝑥𝑒𝑐 𝑚𝑒𝑒𝑡𝑖𝑛𝑔𝑠 𝑠𝑡𝑎𝑟𝑡 𝑤𝑖𝑡ℎ 𝐴𝑉 𝑐ℎ𝑎𝑜𝑠. 𝑍𝑜𝑜𝑚 𝑤𝑜𝑛’𝑡 𝑐𝑜𝑛𝑛𝑒𝑐𝑡. 𝐴𝑢𝑑𝑖𝑜’𝑠 𝑚𝑢𝑡𝑒𝑑. 𝑊𝑟𝑜𝑛𝑔 𝑖𝑛𝑝𝑢𝑡. 𝑃𝑃𝑇 𝑖𝑠𝑛’𝑡 𝑠ℎ𝑜𝑤𝑖𝑛𝑔 𝑢𝑝 𝑜𝑛 𝑠𝑐𝑟𝑒𝑒𝑛. 𝐴𝑔𝑎𝑖𝑛.” The … Read More

73% of CISOs Admit… Security incidents due to unknown or unmanaged assets is a huge headache
Once upon a time, the CISO was the firewall champion – emerging from deep within the IT trenches. Networking, servers, patching, endpoint security – these were their domains. And they’ve come a long way. From tech specialists to boardroom leaders, today’s … Read More
The Silent Breach: A Story of Security at the Brink
Logan Carter* has a recurring nightmare. One from his last job. Logan refused to let this nightmare repeat itself at his new job—where he was responsible for even more critical infrastructure. His far-edge security infrastructure—thousands of cameras, badge readers, and … Read More
