Logan Carter* has a recurring nightmare. One from his last job.
The Nightmare.
The first sign of trouble wasn’t an alarm. It was silence.
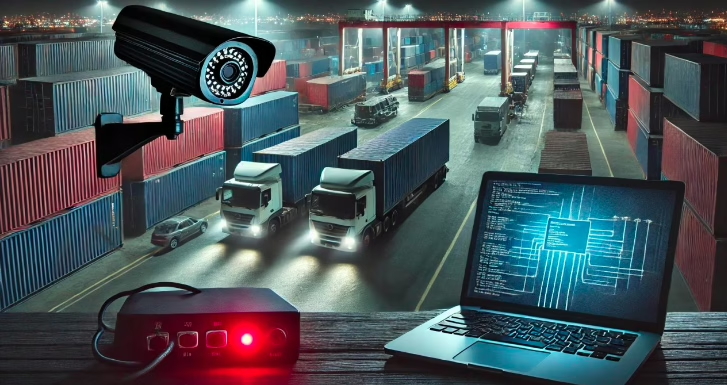
At his previous job—a sprawling global logistics hub where cargo worth billions moved daily—everything ran like clockwork. Security cameras, RFID scanners, and IoT sensors kept constant watch. Nothing slipped through unnoticed. Or so they thought.
Then, on a quiet Tuesday morning, a single security camera at Dock 13 went dark.
No one noticed.
With thousands of devices in the ecosystem, one offline camera barely registered as a blip. But beneath the surface, something far more dangerous was unfolding. An unseen hand had reached into the network.
A small gap—just a single unpatched firmware vulnerability—was all the attacker needed. They slipped in, ghostlike. Within minutes, they pivoted across devices, rewriting access logs, disabling motion sensors, and manipulating security feeds.
Then, in the dead zone they created, they struck.
By the time security teams realized what had happened, millions of dollars in high-value pharmaceuticals had vanished. No alarms. No traces. Just an empty dock and falsified system logs that showed nothing unusual.
Forensic teams later uncovered the truth: one outdated, unsecured edge camera had been the weak link. A single point of failure had spiraled into a multimillion-dollar catastrophe.Logan refused to let this nightmare repeat itself at his new job—where he was responsible for even more critical infrastructure.
His far-edge security infrastructure—thousands of cameras, badge readers, and sensors—was a ticking time bomb. Legacy tools showed “green” across the board, but Logan knew the truth: outdated firmware, unmonitored devices, and blind spots made the company vulnerable.
A recent near-breach had been a wake-up call. They had discovered a hole in an edge device—by accident. But Logan knew luck wasn’t a strategy. He needed predictive, AI-driven edge security before a real disaster struck.
So, he walked into the CIO’s office to make his pitch.
The Pitch.
Emma Reynolds, his CIO, was skeptical. “Logan, we already have security tools in place. Our budget is stretched thin. Why should we prioritize this?”
Logan took a deep breath. He didn’t present slides. Instead, he painted a picture:
” Imagine this: A hacker gains control of just one badge reader at a remote site. No alarms, no alerts—until it’s too late. They unlock doors, access secure areas, exfiltrate data. The board demands answers. We scramble, but the damage is done. Now imagine the headlines: ‘Security Breach Shuts Down Global Operations.’ ”
He let that sink in. Then, he flipped the scenario.
“Now, imagine we have an AI-powered tool that detects vulnerabilities before hackers exploit them. It flags anomalies, patches firmware, and blocks access before a breach happens. No headlines. No crises.”
Emma exhaled. “So, you’re saying this isn’t just about monitoring—it’s about predicting threats before they happen?”
Logan nodded. “Exactly. We don’t need another monitoring tool. We need an edge security intelligence platform that keeps us ahead of attackers. Waiting for a breach costs millions. Acting now costs a fraction.”
Silence. Then Emma spoke: “Approved. Get it done.”
Beyond Firewalls: The Future of Security
Logan didn’t win the budget by drowning his CIO in features. He won by making her feel the risk, see the potential disaster, and experience the solution—before it ever happened.
In today’s world, security isn’t just about firewalls and passwords—it’s about securing the far edge, where physical and digital threats collide.
Instead of waiting for failures or reacting to breaches, organizations need predictive edge security platforms that detect risks before they become disasters.
- AI-driven insights could flag outdated firmware and issue automated patches before vulnerabilities are exploited.
- Real-time visibility into edge assets would have highlighted the camera’s downtime, triggering an alert before attackers could act.
- Automated compliance tracking would ensure every security device remains within policy, eliminating weak links in the system.
Logan’s nightmare wasn’t fiction—it was a warning.
The question is: Will your organization listen before it’s too late?