Logan Carter* has a recurring nightmare. One from his last job. Logan refused to let this nightmare repeat itself at his new job—where he was responsible for even more critical infrastructure. His far-edge security infrastructure—thousands of cameras, badge readers, and … Read More
Daily Archives: April 11, 2025
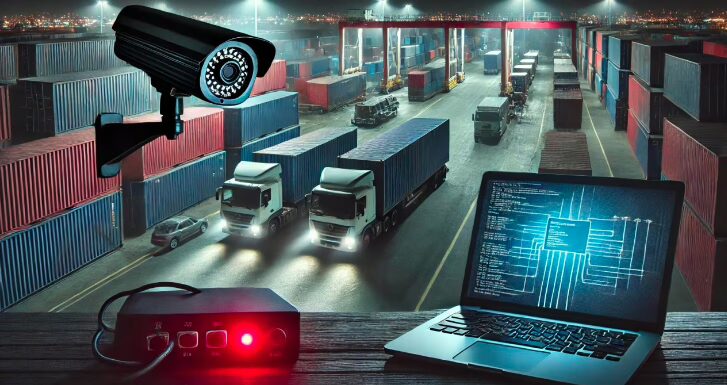
The Silent Breach: A Story of Security at the Brink
Tags: AI, AI & ML driven Automation, AIoT, Alerts & Actions, Asset Ledger, asset management, Automation, Certificate Management, compliance, Cyber Security, cybersecurity, dashboards, Deep learning, downtime, Edge Computing, edge device lifecycle management, Edge Intelligence, edge operations, edge security, enterprise integration, enterprise integrations, firmware update, Industry Solutions, IoT, monitor health & remediate, monitoring, Operational Teams, OT Security, OT teams, Password Rotation, Performance Analytics, Physical Security, PhysSec, predictive analytics, predictive maintenance, proactive maintenance, remote management, remote monitoring, ROI, scalable, scheduling, SmartHub, SmartHub DEFEND, SmartHub INFER, SmartHub.ai, Unified edge management, Uptime, Usage & planning insights, Utilities, visibility, Vulnerability Risk Score
